Ensuring application security from design to operation with DevSecOps.
Security and Privacy
Data Breach Prevention: Strategies For Proactive Cyber Defense
Data breach prevention techniques help businesses reduce existing threats or recognize potential risks before they result in a breach.
Zero-Knowledge Proofs and Their Role within the Blockchain
An examination of the intricate world of zero-knowledge proofs and how they may be used to enhance blockchain security and privacy.
Security Challenges of Intent-Based Networking
Intent-based networking allows operators to describe the high-level intent of what they want a network to do.
Age Verification Systems Will Be a Personal Identifiable Information Nightmare
Online age verification requirements for websites are a disaster for privacy, and pose a cybersecurity risk.
From Open Access to Guarded Trust
Engineers stand at a unique confluence, where the exhilarating promise of innovation meets the sobering responsibility of trust stewardship.
Technical Perspective: Tracing the Network Traffic Fingerprinting Techniques of OpenVPN
OpenVPN Is Open to VPN Fingerprinting
Lattice-Based Cryptosystems and Quantum Cryptanalysis
LLM Hallucinations: A Bug or A Feature?
On the Difference between Security and Safety
LLMs’ Data-Control Path Insecurity
The Dangers of Digitization, and The Importance of Data Backup
Maximizing Power Grid Security
Developer Ecosystems for Software Safety
Perspectives on AI from Around the Globe
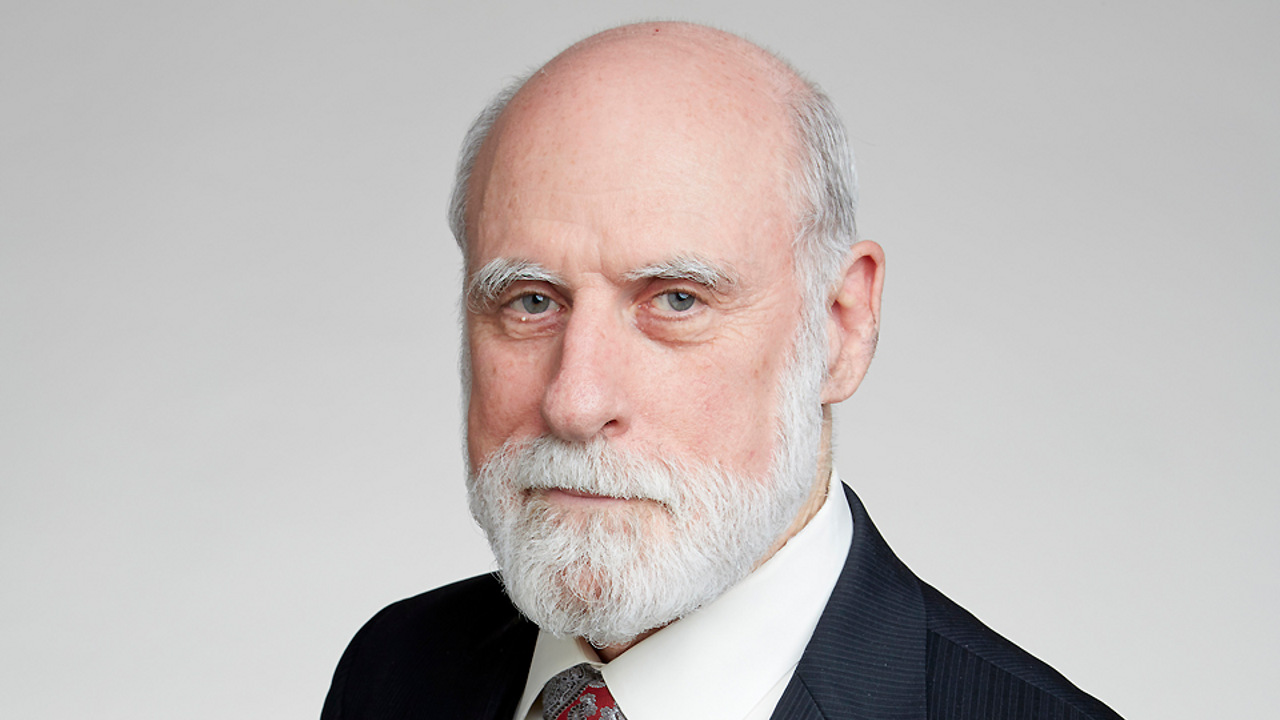
In Memoriam: Ross Anderson, 1956-2024
The Risks of Source Code Breaches
The Return of Age Verification Laws
Shape the Future of Computing
ACM encourages its members to take a direct hand in shaping the future of the association. There are more ways than ever to get involved.
Get InvolvedCommunications of the ACM (CACM) is now a fully Open Access publication.
By opening CACM to the world, we hope to increase engagement among the broader computer science community and encourage non-members to discover the rich resources ACM has to offer.
Learn More